What Happened: A pseudonymous X user known as cprkrn recovered 5 BTC, worth roughly $400,000 to $500,000, from a wallet that had been locked since April 2015. Claude did not break Bitcoin’s encryption. It found an older wallet backup the owner had forgotten about and patched a bug in the open-source tool he was already using.
The story is everywhere on X and r/artificial today, and most of the framing is wrong. Claude AI did not “crack” Bitcoin.
It did not brute-force anything. It did something far less cinematic and, honestly, more useful to think about if you have ever lost a wallet of your own.
A user named cprkrn lost access to a Bitcoin wallet in 2014 or 2015. The reason he gives is that he changed the password while stoned and immediately forgot what he had typed. The wallet sat untouched on the chain from April 1, 2015 until May 13, 2026, when the funds were finally swept out.
The way I see it, the interesting question is not whether AI defeated Bitcoin. The cryptography held. What the cryptography did not protect against was a clever assistant rummaging through a decade of old college files and finding the one thing the owner had missed himself.
This article walks through what Claude really did, why the viral headline misses the point, and whether you should try the same thing with your own lost wallet.

What Actually Happened
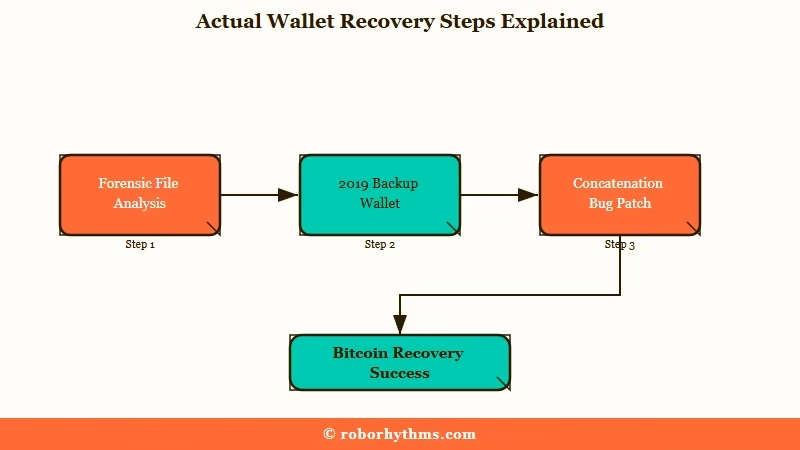
The Claude Bitcoin wallet recovery is a forensic file-search win, not a cryptography break. The owner had every clue he needed scattered across an old computer. Claude found the pieces, fixed a bug in his recovery tool, and ran the working decryption.
Cprkrn announced the recovery in a thread on X that quickly hit the front pages of Tom’s Hardware, Decrypt, and The Register on May 13 and 14, 2026. The amount was 5 BTC, valued between $400,000 and $500,000 depending on the source.
Before turning to Claude, cprkrn had spent years trying conventional tools. He estimates 7 trillion password attempts ran through Hashcat and btcrecover combined, and he spent roughly $250 on professional recovery services. Nothing worked.
What is btcrecover: An open-source password recovery tool for cryptocurrency wallets that tries enormous lists of guesses against an encrypted wallet file.
The breakthrough came when he uploaded what he called a “mega dump” of his old college computer into Claude. Files, notebooks, backups, random documents, everything. Claude parsed the dump, located a wallet file from December 2019 that predated the password change, and surfaced a mnemonic phrase scribbled in an old notebook that read, roughly, “lol420fu*thePOLICE!:)”.
That was not the whole fix. Claude also read the source code of btcrecover and noticed that the tool was concatenating a shared key and the password in the wrong order, which is why every previous attempt against the right password had still failed. Claude corrected the logic, re-ran the decryption, and the funds came loose.
What Did Claude Really Do With the Wallet
Claude did two things, and neither of them involved guessing passwords. It performed forensic file analysis on a decade of old data, and it debugged the recovery tool the owner was running.
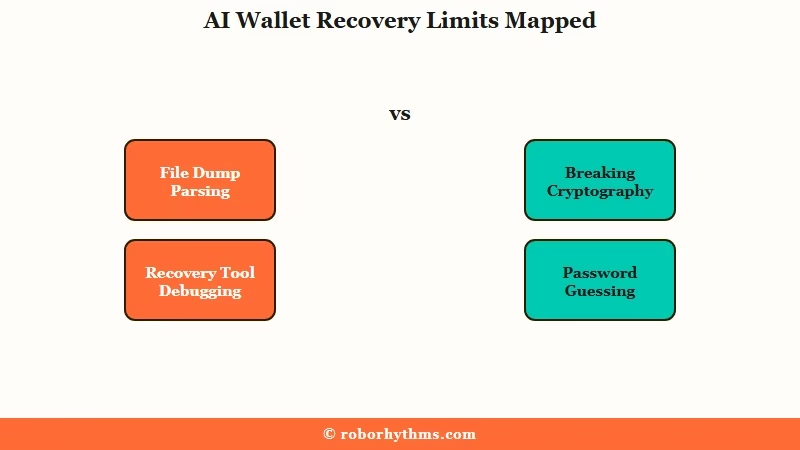
This split matters. Most readers see “AI cracked a Bitcoin wallet” and assume some kind of brute-force breakthrough. What I take from the published coverage is that this is not what happened, and Anthropic engineers quoted in the reporting have been careful to say so directly.
Here is the actual contrast that helps the story land:
Vague: “Claude cracked the password and got the Bitcoin back.” Specific: “Claude read the user’s old files, located a backup wallet from before the password change, found a candidate password the user had forgotten he wrote down, then noticed a bug in the open-source tool concatenating the shared key and password in the wrong order, fixed the bug, and ran the corrected decryption.”
The second version is what happened. The first version is what people are sharing, and it gives an inflated impression of what current AI can do against real cryptography.
What is a P2PKH wallet: A legacy Bitcoin address format used before 2015 that stores private keys in a local wallet file, often protected by its own password independent of any seed phrase.
The wallet in question was a P2PKH file, the format common for early Bitcoin holders. Modern HD wallets with a 12 or 24 word seed phrase work differently, and the recovery path here would not map to them cleanly.
Why This Is a Bigger Deal Than It Sounds
The real lesson is that AI is now competent at long-tail forensic work that previously required a specialist. That is a bigger shift than any single Bitcoin recovery.
What strikes me about the technical write-up is how mundane the steps are. Open old files. Identify wallet format.
Read existing recovery tool. Trace a logic bug. Run it.
A capable software engineer with three weeks and the same files could have done this. The difference is that Claude did it in one sitting, for the cost of a few API calls.
The implication for the rest of the industry is what gets undersold. Coverage of agentic Claude workflows, including the autonomous Claude Code setups that more developers are running, suggests this multi-step debugging is becoming a daily-use pattern. The Bitcoin recovery is a flashy example of a much broader capability.
It is also worth saying that the model’s willingness to read someone else’s broken open-source code, propose a patch, and explain the bug in plain English is what made the recovery work. Without the btcrecover fix, every other piece of the puzzle would have stayed useless.
| What Claude is good at | What Claude is NOT good at |
|---|---|
| Parsing large unstructured file dumps | Breaking modern cryptography |
| Spotting bugs in known open-source code | Guessing a 20-character random password from nothing |
| Cross-referencing notebooks, screenshots, and text files | Recovering wallets with zero remaining clues |
| Running corrected decryption logic step by step | Replacing a hardware wallet’s secure element |
I’d argue this is the right mental model for AI-assisted recovery in general, and probably for AI-assisted forensics across other domains too.
How Did the Owner Lose Access in the First Place
The owner changed his wallet password while intoxicated and immediately forgot what he had typed. That detail is the entire reason this story is shareable, and in my view it is also the most common pattern behind every “lost crypto” tale that ends without a recovery.
Cprkrn has been candid about the cause. He was a college student in 2014 or 2015, the wallet held 5 BTC at the time (a fraction of today’s value), and he changed the password during what he describes as a stoned moment.
The new password felt clever in the moment. Next morning, it was gone.
This is not an edge case. Surveys of self-custody users repeatedly find that “I forgot the password” beats “someone hacked me” by an order of magnitude as the cause of permanent loss. Hardware failure, lost seed phrases, and forgotten encryption all sit in the same broad category of human error.
The recovery worked because cprkrn had kept the old machine, kept the old wallet backups, and had written the original password down somewhere in a notebook he never threw out. If any one of those had been missing, Claude would have had nothing to work with.
Can Claude Recover My Lost Bitcoin Wallet Too
It can help only if you still have meaningful historical data on the original machine or in old backups. No AI in 2026 can guess a strong password from a blank starting state.
Here is the honest version of what Claude can and cannot do in a lost-wallet scenario:
- If you still have the original computer or a full disk image of it, Claude can do useful forensic work on old files, screenshots, and notes.
- If you have a partial seed phrase or password fragment, Claude can help generate plausible variants and check them against the wallet.
- If you used an open-source wallet or recovery tool, Claude can review the source for known bugs or misconfigurations.
- If you have nothing other than the wallet address, Claude is no more useful than any other tool. The math has not changed.
The owner of the 5 BTC had categories 1, 2, and 3 all working in his favor. That is a rare combination, and most “I lost my Bitcoin” stories on r/Bitcoin do not look anything like it.
I’d also recommend not setting your expectations from the viral framing. The recovered wallet is real, but the story is a survivor-bias example, not a template. For every cprkrn there are thousands of holders whose lost coins are genuinely unreachable.
Is It Safe to Upload Wallet Files to an AI
It is not safe to upload an unencrypted wallet file, raw seed phrase, or private key to any cloud AI service. That includes Claude, and the cprkrn case is not a good template here.
This is where the underserved angle of the story sits. Anthropic’s terms of service allow them to retain user inputs for safety review and model training, depending on plan and settings.
Cprkrn appears to have uploaded a “mega dump” that may have contained private key material in some form. The recovery worked, but the privacy trade-off is not free.
The safer version of the same workflow, if you want to attempt it with your own data:
- Run a local, open-weight model (a Llama 3 or Qwen variant via Ollama or LM Studio) on your own machine so the wallet file never leaves it.
- Upload only metadata to a cloud model, file names, password hints, scraps of recall, and let the cloud AI propose strategies without seeing the keys themselves.
- Use a clean, offline computer to run any real decryption attempts.
- Move recovered funds immediately to a new wallet with a freshly generated seed phrase.
Recent Anthropic research has also surfaced odd behavior around model self-awareness, including the Claude tested-detection finding from interpretability work last week. That is not a privacy issue on its own, but it underlines that you do not fully control what a hosted model does with your inputs.
The way I see it, the upload-everything strategy worked exactly once on a public stage. For a normal reader sitting on a wallet that might be worth real money, the local-model variant is the responsible default.
What This Means for You
The Bitcoin headline is bait, but the underlying capability is worth your attention. AI-assisted forensic file work has crossed the line from “research demo” to “thing someone uses to recover $400,000 in an afternoon.” That generalizes well beyond Bitcoin.
If you have an old computer in a closet that might be holding something valuable, an Apple Notes export from a decade ago, a forgotten email account, or any other archive you have never been able to mine yourself, this is a reasonable moment to revisit it. The pattern that worked for cprkrn (dump the data, let a capable model parse and cross-reference, ask specific questions about what you might be looking for) is now a real workflow.
For developers, the second-order story is that Claude read and patched a known open-source recovery tool in passing. As AWS AgentCore Payments coverage suggests, this “AI as a working software engineer” pattern is showing up in production systems faster than most teams have planned for.
For everyone else, the practical takeaway is to keep your old machines, your old notebooks, and your old hard drives. The data you wrote down years ago is now searchable in ways it was not before. That cuts both ways for privacy, and it is worth thinking about before you upload the wrong folder.
What Comes Next
Expect a wave of similar “AI recovered my lost X” stories over the next quarter. Some will be real, some will be staged, and most will be misunderstood as cryptography breaks when they are really file-organization wins.
Anthropic has not officially commented on the cprkrn recovery, and there is no sign that this is part of any product push. It looks like an organic case study, which is exactly the kind of demo that ages well. I’d watch for two things in the coming weeks.
First, whether any professional crypto recovery services start advertising Claude-assisted forensics as a paid offering. The economics suddenly look different if a $250 manual attempt can be replaced with a $20 API run. Second, whether Anthropic publishes any guidance on safe handling of high-value file uploads, since the cprkrn case sets a precedent that will be misread.
The viral version of this story will be forgotten in a month. The capability it points at will not.
