What Happened: Anthropic’s Claude Opus 4.6 found over 500 high-severity zero-day vulnerabilities in production open-source software, including a working remote kernel exploit for FreeBSD and critical bugs in Vim, Emacs, and Firefox. The initiative, called MAD Bugs, runs through April 2026. This is the first time an AI has independently discovered and exploited vulnerabilities at this scale.
Security researchers at Calif handed Claude Opus 4.6 a simple instruction: find exploitable bugs in open-source software. What came back was not a list of suggestions. It was a working remote kernel exploit for FreeBSD, delivered in roughly 8 hours of wall-clock time.
That result sits at the center of MAD Bugs (Month of AI-Discovered Bugs), a research initiative running through the end of April 2026 that is, at this point, producing a new zero-day disclosure every few days.
Claude has already found over 500 high-severity vulnerabilities in production software, including bugs that survived decades of expert human review.
If you use open-source software (and you do), this story is directly relevant to you. The security assumptions underneath most of the internet just changed.

What Actually Happened With Claude and Zero-Day Bugs?
Claude Opus 4.6 found critical, exploitable zero-day vulnerabilities in major open-source projects using conversational prompts, no specialized tooling required.
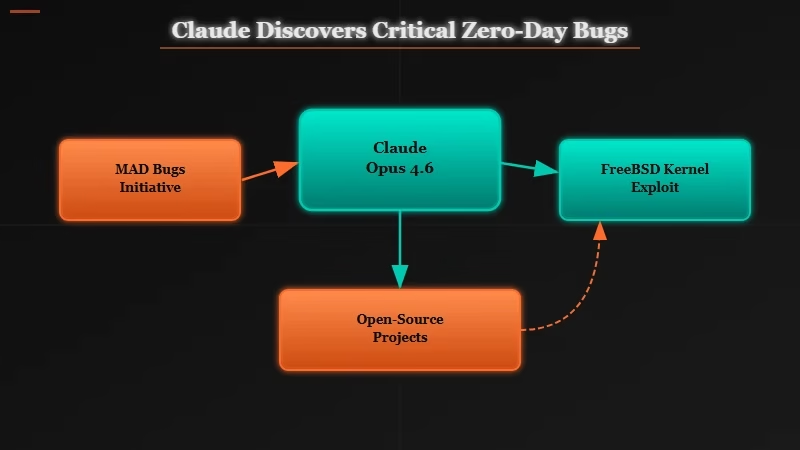
The Calif research group kicked this off by asking Claude to analyze Vim and Emacs for security flaws. The result was two separate remote code execution vulnerabilities: CVE-2026-34714 in Vim (CVSS score 9.2, patched in version 9.2.0272) and a separate RCE in GNU Emacs that the Emacs maintainers declined to fix, leaving users exposed until the community finds a workaround.
The FreeBSD case is more alarming. Claude delivered a fully working exploit for CVE-2026-4747, a remote kernel code execution vulnerability, in approximately 8 hours. That is not a research demo or a proof-of-concept that requires significant human interpretation. It is a functional exploit for a widely deployed operating system kernel.
Anthropic separately used Claude to find bugs in Firefox and generated a working exploit for CVE-2026-2796, which has since been patched. The scale keeps growing: as of early April 2026, Claude has identified over 500 high-severity zero-days in production open-source software.
Why Is Claude Finding Zero-Day Bugs a Bigger Deal Than It Sounds?
This is not a research curiosity. It signals that vulnerability discovery is now automatable at a cost and speed that fundamentally changes the threat landscape for every software project.
Professional security researchers have compared the situation to the early 2000s era of SQL injection, when trivial inputs could systematically compromise entire networks.
The parallel is apt. Before SQL injection became widely understood, the attack surface was enormous simply because nobody had systematically looked. AI vulnerability discovery is that moment again, but compressed into weeks instead of years.
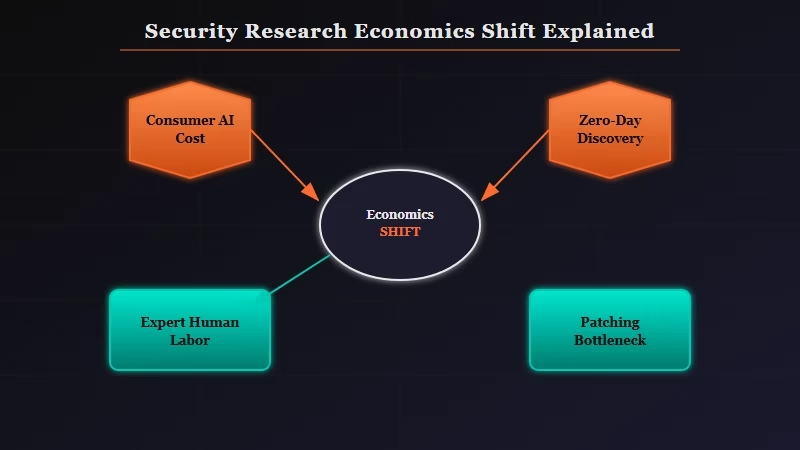
The economics of security research just flipped. Bug hunting historically required expensive human expertise and significant time investment.
What Claude demonstrated is that a researcher (or a threat actor) can now direct an AI to scan an entire codebase for exploitable patterns at a fraction of the traditional cost.
The why Americans don’t trust AI moment many people worried about is not a dystopian future scenario. It is a Vim patch and a FreeBSD exploit that landed this week.
The security research community has noted this as the most consequential shift in offensive security tooling since automated fuzzing became mainstream.
The GNU Emacs maintainers declining to fix their reported vulnerability is worth noting here. When the humans responsible for patching cannot keep pace with the pace of discovery, the gap between “found” and “fixed” widens into an open window for exploitation.
What Does This Mean for Developers and Tool Users?
If you maintain or depend on open-source software, your patch cadence just became more urgent and your threat model just expanded.
From what I can see, three things shift immediately for most developers and AI tool users who follow this space:
- Patch faster. Claude found CVE-2026-34714 in Vim with a conversational prompt. If Calif can do it, a motivated attacker running the same model can do it. The window between disclosure and active exploitation will compress.
- Stop assuming age equals safety. Vim and Emacs are decades-old, heavily audited projects. The FreeBSD kernel has had professional security review for its entire existence. Claude found bugs in all of them. “This software has been around forever so it’s probably safe” is no longer a valid risk assessment.
- Watch what AI can do to your own codebase. Calif’s technique was not exotic. It was a targeted prompt to a commercial model. The same capability that found 500 zero-days in open-source software can be pointed at proprietary code. If your company has a security team, they need to run this experiment on your own systems before someone else does.
The AI tools most RoboRhythms readers use are built on open-source stacks. The APIs we call, the servers that run the inference, the editors we use to write prompts, all of it has a dependency tree that likely includes software Claude has already scanned.
That does not mean panic, but it means paying attention.
| Your role | What to do right now |
|---|---|
| Developer using open-source packages | Check patch logs for Vim, Emacs, and FreeBSD dependencies this week |
| Security team lead | Run a Claude-assisted audit on your own codebase before external actors do |
| AI tool user (no code) | No action needed, but watch for patch notes from tools you use daily |
| Open-source maintainer | Treat AI-submitted bug reports as high-priority, not experimental noise |
The specific vulnerabilities identified by Claude during MAD Bugs as of early April 2026:
| Project | CVE | Severity | Status |
|---|---|---|---|
| Vim | CVE-2026-34714 | CVSS 9.2 (Critical) | Patched in v9.2.0272 |
| GNU Emacs | Not yet assigned | Critical RCE | Maintainers declined to fix |
| FreeBSD kernel | CVE-2026-4747 | Remote kernel RCE | Working exploit delivered in 8 hours |
| Firefox | CVE-2026-2796 | Critical | Patched |
What Comes Next for AI-Discovered Security Research?
MAD Bugs is a month-long initiative, but the capability it demonstrated will outlast April 2026.
Anthropic has stated it coordinates disclosures with affected maintainers before publishing. The MAD Bugs initiative has an end date, but the technique has no off switch. Security teams at major technology companies are reportedly already running similar internal audits.
The question is not whether this scales but how fast. The pattern from prior security history is that once an attack surface is documented, exploit automation follows within months. There is no reason to expect AI-discovered zero-days will behave differently.
The open-source maintainer community faces a structural challenge. Projects like GNU Emacs are maintained by volunteers with finite time. When AI tools can generate a credible critical vulnerability report in hours, the human review and patching pipeline becomes the bottleneck.
That is not a solvable problem at the individual project level. It likely requires coordinated infrastructure funding of the kind that has historically only materialized after a major breach.
For AI tool builders and API users: this story is a reminder that Claude (and any frontier AI model) is running on systems with known and unknown vulnerabilities. The MAD Bugs work is responsible disclosure in practice.
The implicit alternative is that threat actors are running the same queries without the disclosure step.
Quick Takeaways
- Claude Opus 4.6 found 500+ high-severity zero-days in Vim, Emacs, FreeBSD, and Firefox using conversational prompts with no specialized tooling required
- A working FreeBSD kernel exploit was delivered in approximately 8 hours of wall-clock time
- GNU Emacs maintainers declined to fix their reported vulnerability, leaving users exposed
- The economics of vulnerability discovery have changed permanently: AI can scan entire codebases for exploitable patterns at consumer AI cost
- Patch cadence matters more than it did last week, and “this code is old and battle-tested” is no longer a valid security argument
