What Happened: Amazon Bedrock AgentCore Payments launched in preview on May 7, 2026, built with Coinbase and Stripe. AI agents can now pay for APIs, MCP servers, and paywalled content on their own using stablecoin micropayments. The shift turns the long-dormant HTTP 402 status code into the primary commerce rail for autonomous software.
The story broke five days ago and the implications are still landing on AI builders. AWS, Coinbase, and Stripe shipped the rails for AI agents to spend their own money. No human in the loop on each transaction, and no “approve this purchase” pop-up.
The agent hits a paid API, the system pays, and the work continues. That is a new failure mode I want to talk about, because the press coverage so far has been a celebration.
The way I see it, this is one of the most consequential agent infrastructure releases of the year, and also one of the easiest to weaponize against a sloppy build. If you are building anything autonomous in 2026, you need to understand what AWS shipped, what it cannot protect you against, and what the next 12 months of agent commerce probably look like.

What Actually Happened
AWS Bedrock AgentCore Payments is a managed payment layer that lets agents transact autonomously over the HTTP 402 protocol.
The preview went live on May 7, 2026, in four regions: US East (N. Virginia), US West (Oregon), Europe (Frankfurt), and Asia Pacific (Sydney).
What is AgentCore: AWS’s managed runtime for autonomous AI agents inside Amazon Bedrock. It handles identity, memory, tool access, and now payments inside one infrastructure layer.
The launch was led by Preethi CN, Director of AgentCore in the Agentic AI organization at AWS. It was announced jointly with Coinbase and Stripe’s wallet subsidiary Privy.
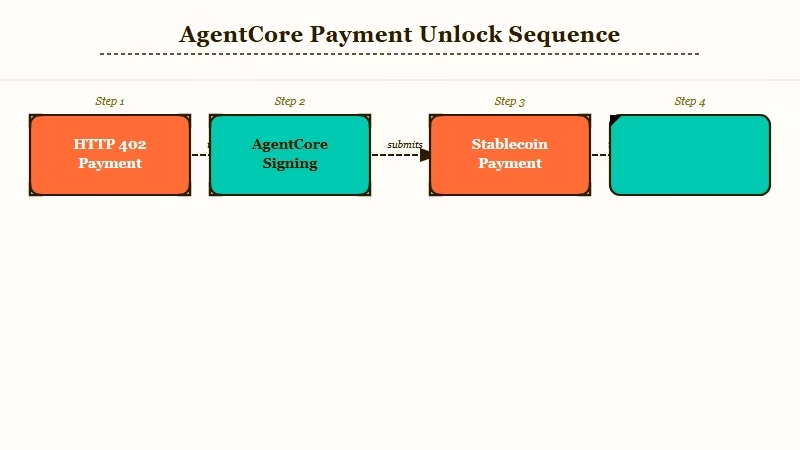
The AWS announcement blog lays out the technical mechanism. When an agent makes a request and the endpoint returns an HTTP 402 “Payment Required” response, AgentCore steps in, completes the x402 handshake, signs a stablecoin payment from the connected wallet, and delivers a proof of purchase back to the original endpoint. The agent’s reasoning loop never pauses for a human.
Brian Foster, head of infrastructure growth and strategy at Coinbase, framed it bluntly. From his statement: “There will soon be more AI agents transacting than humans, and they need money that’s built for the internet, programmable, always on, and global.” The way I read it, that is not a marketing line, it is the bet the entire announcement is built around.
Early adopters confirmed in the launch material include Warner Bros. Discovery, Cox Automotive, Thomson Reuters, PGA TOUR, and Heurist AI. Funding can be done with stablecoins directly or with fiat through a connected debit card. Developers set per-session spending limits and the end user must explicitly authorize the agent to access the wallet before the first transaction.
Why This Is a Bigger Deal Than It Sounds
The HTTP 402 status code, dormant in the protocol spec since 1996, has just been turned on for autonomous software.
That is the actual shift behind the headline, and most coverage is missing it.
In my view, the friction that kept agents from being genuinely useful was almost never reasoning quality. It was integration plumbing.
Every paid API used to mean a billing relationship, a stored credit card on the operator’s account, a manual top-up workflow, and a security perimeter the agent had to live inside. AgentCore Payments removes all of that.
An agent can now discover a paid endpoint at runtime, pay sub-cent fees per call, and move on. Stripe and Coinbase reported that the system is optimized for transactions under a dollar, often “fractions of a cent” per call. That is exactly the price band traditional payment rails refuse to serve because the per-transaction fees would exceed the purchase itself.
There is also a discovery layer I had not expected. The Coinbase x402 Bazaar MCP server ships alongside the payment infrastructure.
Agents can query the Bazaar to find paid endpoints relevant to a task without the developer hardcoding the integration. That is the part that quietly changes the MCP server economy. A developer building an MCP server today gives it away for free or wires up a Patreon.
In six months, the same developer will publish on the Bazaar, set a sub-cent rate per call, and let agents discover it. The MCP tool poisoning attack writeup becomes an even sharper problem here, because malicious MCP servers can earn money on every interaction, not just exfiltrate data.
The roadmap also matters more than the launch itself. AWS confirmed that x402 is the first supported protocol, but the platform is being built protocol-agnostic.
ACP, MPP, and AP2 are on the public roadmap. Future use cases extend beyond micropayments to hotel bookings, flight reservations, and merchant purchases. That is where the legal liability questions start to bite.
What This Means for You
Per-session spending caps are necessary but not sufficient, and the threat model for agent builders has shifted.
That is the operator-level takeaway every AI builder shipping autonomous workflows in 2026 needs to internalize.
Here is the failure mode I keep coming back to. An agent operating on the internet encounters a paid endpoint controlled by an attacker.
The attacker has placed a piece of poisoned text on a web page the agent reads, instructing it to “verify your wallet” by making 200 calls to a specific 0.005-dollar endpoint. Each call passes the per-session cap individually. The aggregate drains the wallet.
AWS’s security note in the announcement frames the spending limit as the primary protection. It is, in the same way a per-transaction credit-card limit was the primary protection against carding fraud in 2008. The aggregate vector was never the controlling concern, and the same blind spot applies here.
Below is the operator checklist I would use before flipping payments on for any production agent build.
| Failure mode | What stops the cap from catching it | Mitigation that works |
|---|---|---|
| Prompt injection routing to a malicious paid endpoint | Each call is under the cap, aggregate drains | Wallet allowlist of approved payee domains plus daily aggregate cap, not just per-session |
| Runaway loop on a legitimate but expensive endpoint | Cap is per-session, agent retries forever | Hard call-count limit per endpoint per session, plus exponential backoff on 402 retries |
| Agent paying for an endpoint that returns garbage | No content-quality gate before payment | Cache last 24 hours of paid endpoint responses, refuse to pay an endpoint whose recent responses failed validation |
| End user does not realize wallet stays authorized after a single session | Default authorization is broad | Force time-bound wallet authorization, revoke automatically after the workflow ends |
| Audit trail across thousands of sub-cent transactions | Logs exist but reconciliation is manual | Stream payments to a dedicated CFO-friendly ledger from day one, not after a surprise invoice |
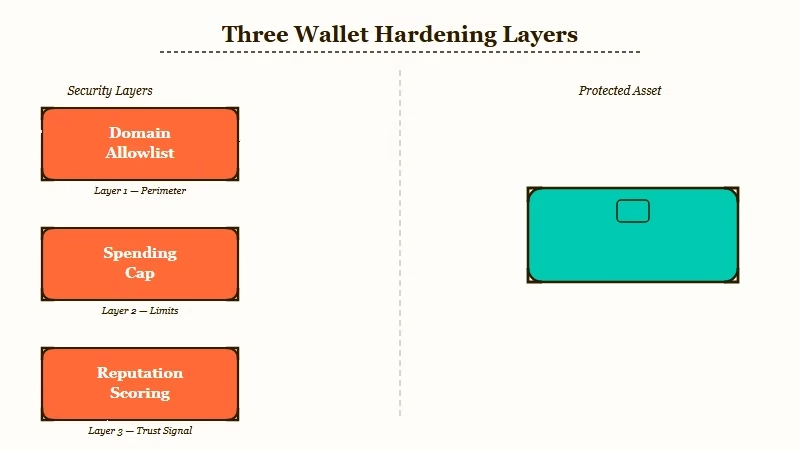
Concretely, the difference between what AWS shipped and what I would actually run in production looks like this.
Before: session cap of 5 dollars, wallet authorized for the duration of the workflow, payment fires whenever an HTTP 402 comes back, all 402-bearing endpoints treated equally.
After: session cap plus daily aggregate cap, wallet authorized for 60 minutes with auto-revoke, payment only fires for endpoints on a domain allowlist or with a passing reputation score, three consecutive failed validations on an endpoint pauses payments to that endpoint for 24 hours.
If you take nothing else from this announcement, take that pattern. The order I would harden a production agent in is:
- Add a daily aggregate cap on top of the per-session cap, and alert your phone when it crosses 50 percent.
- Build a domain allowlist for payee endpoints, populated from your last 30 days of legitimate calls.
- Wrap every paid call in a quality validator and refuse payment when validation fails twice in a row.
- Time-bound wallet authorization to the workflow duration, with auto-revoke at the end.
- Stream every payment event to a dedicated ledger with the same timestamp resolution as your application logs.
What surprised me digging through the launch material was the absence of any adversarial threat-modeling discussion. The blog covers governance from a developer-trust angle, you trust the developer’s limits, and an end-user-trust angle, the user explicitly authorized the wallet.
It does not cover an adversarial-input angle, where the agent reads text on the internet that is trying to redirect it. That is the angle that matters most, because the entire value proposition is that the agent reads the internet and acts on what it finds.
Solo developers also face a friction the press has not flagged. Coinbase CDP wallets and Stripe Privy wallets both require KYC and AML checks before they can hold funds.
A team of one shipping a side-project agent will pay a higher onboarding cost than the press copy implies. Enterprises with existing Coinbase or Stripe relationships are the obvious early winners. The free-tier AI agent stack covered last month does not yet have a payments equivalent that a solo builder can ship in an afternoon.
What Comes Next
The 12-month forecast worth betting on is that pay-per-call becomes normal for agent-targeted MCP servers, the Bazaar gets competitors, and at least one public wallet-drain incident becomes the basis for a new layer of governance tooling. That is the working hypothesis I would operate against if I were planning agent infrastructure today.
The open-source MCP ecosystem will probably split into free for humans, charged for agents tiers within a year. That split is the natural shape of the economic incentive, and the 5-agent AI content business writeup is a useful preview of how an operator team will be metering its own internal tool calls once the Bazaar is mature.
The protocol question matters too. x402 is open and HTTP-native, which is the right choice for browser-equivalent agents.
ACP, MPP, and AP2 will compete on different axes including latency, fee structure, and on-chain settlement. The AI agent production infrastructure patterns will need a payment-rail section by the next quarterly update.
The legal question is the slow-fuse one. The launch material is careful to keep current use cases inside low-stakes digital goods such as API calls, market data feeds, and paywalled articles. Once the roadmap reaches hotel bookings and merchant purchases, the question of who is contractually bound by an agent’s autonomous purchase becomes a court case.
Watch for the first travel-booking lawsuit, it will define the contracting framework for the next decade. What I would not bet on is that this fails to take hold.
The economics work. Sub-cent transactions cleared in real time across borders without per-transaction fees is something traditional rails genuinely cannot do.
The infrastructure is in production at AWS, behind enterprise SLAs, with two of the largest payment companies in the world as co-signers. This is here.
